Automotive Security: How Safe Is The Automotive World Of Tomorrow?

Can you trust automotive security? What are the main challenges of the automotive development process? How to make it safer? Learn more here…
Automotive Society And Its Security
People have always been worried about the question of automotive security. It is not surprising considering our reliance on different types of vehicles. Globalization depends on how efficient the machines are. The transportation of people and cargo is essential to prosperity and further development. But automotive development process turned machines into something more than the means of transportation.
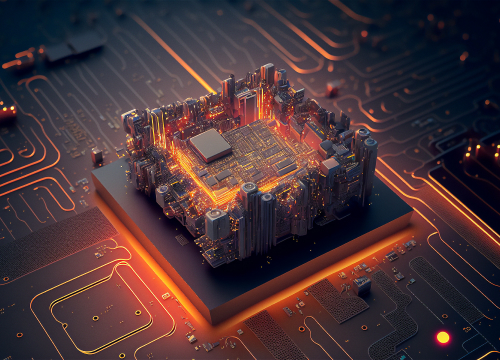
The computerization of vehicles has enhanced the efficiency of automobiles. Some dashboards can substitute phones, laptops, maps, radios, and some other things. The latest innovations let you relax while your car drives on autopilot. And there are many other potential possibilities of improvement hidden in the future. Is it safe, though?
Automotive development improves the comfortability of the driving process for the people inside. However, it also creates an environment for new threats.
Security Threats Of Automotive Development
The computerization of cars means automotive software engineering, codes, programming, and… risks of hacking. The era of digitalization and embedded software makes us worry not only about carjackers but hackers as well. A modern electric car has millions of code lines to support all the perks we love so much – WiFi, GPS, Driving Assistance, etc. Besides, we can connect our smartphones and computers to our car, keeping our data in all the things around us (the Internet of Things). That is where the new security threats of automotive development appear.
Hackers can get access to the cars and the personal information kept within. They can also get control of your dashboard, breaks, or steering system, to name but a few. With the further advancement of automotive development, we can expect a more digitalized driving process, and therefore – more opportunities for hackers.
Other security issues of automotive development might be less dramatic. To create those millions of code lines for a car is not an easy task. Automotive software engineering might be done poorly sometimes, resulting in some system flaws.

Ensuring Security for Automotive Development
What are the ways to prevent the risks of automotive software development?
Security By Design In Automotive Development
It is better to start paying attention to essential details from the first stages of automotive software development. Security by design refers to the process of ensuring security from the very beginning. It is necessary to understand how hackers think to prevent their attacks. Thus, developers should make a full-length automotive security risk assessment to find potential security failures in the architecture and design of the software system. This way, software engineers should be able to decrease the risk level of the automotive system.
Safer Embedded Software Development
After the automotive security risk assessment and planning of the future design, the actual software development starts. To increase safety, developers should work hard on cyber-security implementation. For example:
- Cyber-security in code – developers should possess a great deal of knowledge in the cyber-security area to find safety solutions for the automotive system.
- Firewalls help create much safer embedded software; the development of firewalls improves the overall security by controlling traffic into the ECUs (electronic control units).
- The encryption of the software puts an extra layer of protection against hacking attacks.
- A threat detection system makes the system safer, detecting dangerous anomalies or incoming viruses and stopping them from harming the embedded software on your vehicle. The development of detection systems is necessary for automotive security risk assessments, as it shows what methods intruders are using to get in.
- Developers face a lot of mistakes and difficulties along the way. That is why the occasional code review is important, as it allows closing the security gaps.
The Final Stage Of Ensuring Security
So, the vehicle is on the market. It does not mean the end of the work. Until that vehicle stops being produced, there is always a chance for some upgrade. Despite all those automotive security risk assessments and all the code testing, new issues and threats will appear. Hackers might come up with new methods of breaking into the system. So, the need for development services is always there.
Conclusion
The automotive software systems produce opportunities for hackers to steal data or take control of the vehicles. However, it is not something we can avoid. Technological advancement is about making our life easier to live. Digitalization and interconnectedness are the features of this new comfortable world. And some people might use it against others.
Automotive security is feasible. It takes a lot of work, but it is feasible.
If you want to make your project secure, contact our experts. Sirin Software makes it feasible.
And if you want to be on board with current technology, make sure to check our blog.