Within the last few years, the usage of various electronic devices has become widespread. Now, we can’t imagine our lives without some of them. They might be our helpers at home, on the road, or at work. In fact, we are sometimes so used to them we don’t think anything can ever happen to them or any harm can come to us. But the truth is that embedded Linux devices have vulnerabilities. Thus, their security should be no less of a priority than that of our car or house.
You can assume that any device can be compromised sooner or later. The devices often control transportation, utilities, communications, and other parts of our lives. Cyber-attacks on embedded devices can have terrible consequences.
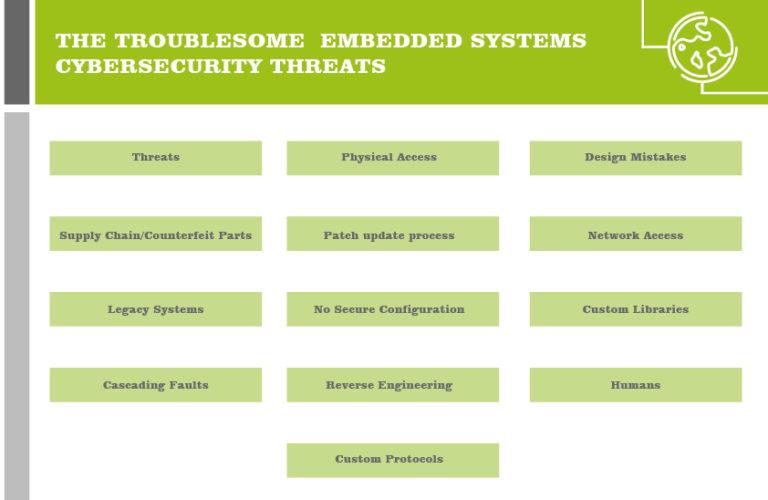
Where does the danger lie?
Some of the dangers to security are related to replication. Embedded devices are generally made in bulk and are identical in their design. This means that if one device has been compromised, all the others can be considered compromised by default.
Another problem is that these kinds of products generally have a long life cycle (approximately 15–20 years). This makes them less and less’ compatible with new security and software updates as time passes.
Considering their wide distribution, the problem of patching also arises. It is quite complicated to have embedded devices patched as remote software allowing updates is generally not implemented by default. Also, many of the devices are directly connected to the Internet, which makes them an easier target for attacks.
How to ensure your device is protected
Looking into the security of embedded Linux devices, you should consider all kinds of interactions. Some dangers are easier to avoid than others, but this doesn’t mean you shouldn’t try. A threat to your device might come externally or internally, and there are some actions that require physical access to the device for execution. To protect against an information breach, there are a few things that can be done:
- Physical security
We already mentioned that sometimes the problem is the enemy within. Your own colleagues can accidentally or intentionally do some harm. The easiest way to prevent this is to limit the number of people having access to the device. Make sure that only those who really need to interact with your device physically have access to it.
Another option, while does not exclude the first one, is to fix the thing in place (if possible). This, of course, does not guarantee that nobody can access it. But it will definitely take some time for them to do that.
- Device access protection
As well as physical access, you might want to restrict the number of people having access to control a device. For example, a two-person rule for accessing security keys is sensible.
- Confidentiality of data
If there is any sensitive information stored in your embedded Linux devices, it should be encrypted. This includes passwords, keys, collected data, etc. This can be a good strategy even if physical access to the device is allowed. You can encrypt the whole data storage device, some directories, or certain files.
- Security updates for a device
You need to ensure that your device can receive security updates whenever required. For this, it needs to have a stable power supply and network access. Additionally, it needs to be compatible with the upcoming updates.
- Monitor the field
Occasionally, new security breaches are discovered in what was previously believed to be a stable and secure system. In Linux-based systems, this happens quite often. Make sure you are aware of those discoveries and that your embedded Linux devices are supplied with a necessary fix as soon as possible.
But why just sit around and wait? You should perform your own security checks every once in a while. That way you will know what is happening within your system and will be able to react immediately if something doesn’t seem right.
- Use certificates
The use of certificates is related to the asymmetric encryption approach. They bind a certain public key to a particular name or its alternate in the form of an email address or a DNS entry. A Certificate Authority (CA) issues a certificate based on the private key generated in your system. If compromised, a certificate can be reissued and revoked. Code Signing certificates are a way of verifying the authenticity of the code within the device.
- Implement a secure boot mechanism
Generally, there is a window for vulnerability during the boot sequence. Most of the approaches for securing a boot with good software images rely on secure hardware: for example, a Trusted Platform Module (TPM) or smart card. This kind of hardware computes a hash that is then compared with data in the secure data storage. If the values are confirmed successfully, the boot proceeds. If something is not right, a signal is sent.
- Restrict external access
If possible, implement access to your embedded Linux devices to only from inside your environment. This might include VPN access, IP restrictions, 2FA authentication, etc. You can also include IPv4 and IPv6 firewall protection as well as removing any non-required services or software.
- Perform crash tests
As you are developing or implementing a device, it’s always better to be the first one to know where you have gaps and to fix them beforehand. For this, you might want to perform some “crash tests” for your device to make sure you didn’t miss anything. If you find any weaknesses, you will be able to fix them before introducing the device into service.
- Hire a security expert
While a development team might do a great job building something, there is a high likelihood they are not aware of every possible threat to a product. Hiring an expert in the matter might be quite costly, but you can develop a security strategy to use specifically for your device. Also, you can hire pentesters from the outside from time to time to ensure compatibility with the latest security standards.
The final word
As you can see, there a few challenges in securing embedded Linux devices. Some of the solutions have their drawbacks or might not be possible under certain conditions. However, it is very clear that security needs to be considered as one of the primary parts of product development as well as the further life cycle. The implementation of a security strategy can be expensive and, therefore, requires consideration. The main objective of your decision should be the necessity to protect information. If you would like to introduce security into your embedded device or receive an expert consultation, feel free to contact our team. We are always ready to help you find the best solution and have deep expetixe in this fiels.

