As you may understand, providing DevOps security involves the integration of certain standards in the processes of planning, development, testing, and deployment of software.
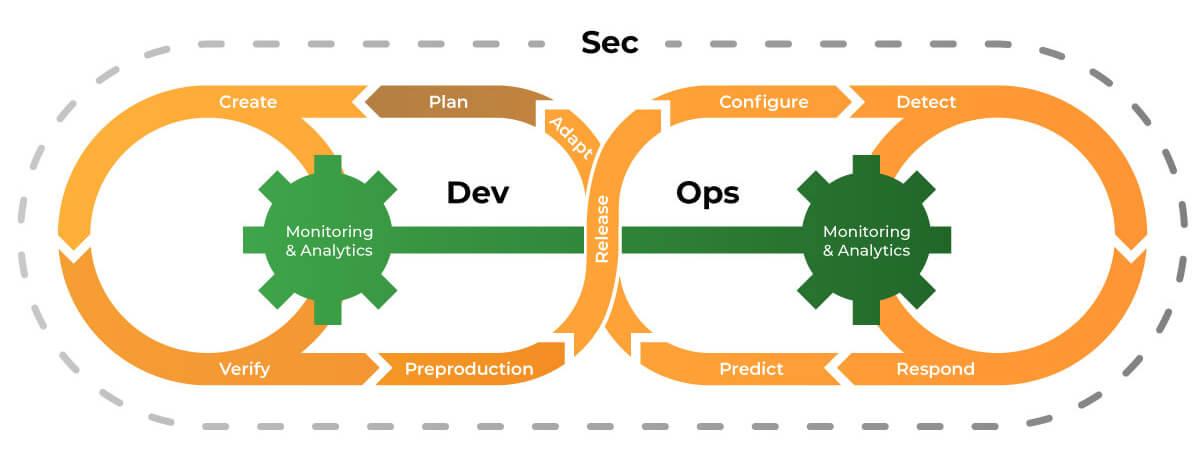
These DevOps security permissions help to deprive the application of many unobvious vulnerabilities long before its release. In contrast, ordinary security professionals usually perform their duties after the creation and implementation of software – for instance, simply by setting up a firewall or installing antivirus/antimalware software.
DevOps Security Automation as the Foundation of End-to-End Safety of Your Business
In fact, most DevOps security best practices are based on automation. This means that in the long run, using DevSecOps, you simplify the task list for both the specialists that create/test your business software and for the tech support department employees.
The Main Principles of DevSecOps Specialists
All in all, five principles for securing DevOps employed by most experts in the field can be noted:
- Composition of a DevOps security checklist that covers all software and hardware components;
- Merging of different teams of experts to ensure safety at all stages of product development;
- Giving preference to readymade APIs instead of developing security solutions from scratch;
- Constant checking of already launched solutions for vulnerabilities;
- Recording of all incidents in the event log for further analysis and work on errors.
DevSecOps vs. DevOps
What about the differences between regular DevOps and security DevOps? For sure, your staff may already have a DevOps specialist. But that is a much wider concept, unlike DevSecOps, which implies a narrower specialization. (Read more: Open-Source DevOps Security Tools that are Used by DevSecOps Experts)
Changes caused by DevSecOps implementation
The traditional security scheme involves the post-implementation of appropriate tools (i.e., after the release of an existing solution).
With security DevOps, as you can understand, the secure team hones software for predefined security standards at each stage of the project life cycle and sends everything that doesn’t meet these standards back to developers.
Without a doubt, the development process when practicing DevOps security and compliance will take a little longer. But this approach will reduce the need for corrections at the stage of active software use, when the detection of vulnerabilities is guaranteed to entail not only downtime but also, possibly, leakage of important data.
DevSecOps benefits
Dev Ops security is a whole system safety culture. Adding safety standards to the existing list of specifications, developers on the one hand get an increased number of requirements for their work; but on the other hand, they have far fewer opportunities to make mistakes (because the clearer the tech reference, the less the chance that the final result won’t meet customer expectations).
As a matter of fact, Dev SecOps focuses on the future because the initial time costs are somewhat larger than those that are typical for the traditional methodology of implementing security solutions.
Thus, you create a long-term efficient solution that will be resistant in the future even to currently unknown threats (if we take firewalls as an example, types of software that only allow valid DevOps security policy packages are more efficient than those that simply use filters for non-admission of prohibited and suspicious content).
Why it is better to find new experts with DevOps security certification rather than re-educate existing staff
Implementing DevOps security best practices never implies expanding the expertise of existing professionals. Usually, all responsibilities related to end-to-end security are taken up by third-party specialists with DevOps security certification who have a global understanding of what to do at each stage of the software life cycle and how to compile the list of standards.
Summary
If you’re looking for a team of experts to introduce DevSecOps into your workflow and boost the security of your project overall – hit us up. We have a team of passionate profiled specialists waiting to take on any project scope and purpose.