“Technology changes super fast, so we need to keep coming up with new and better network systems. The goal is to always be a step ahead, creating networks that work really well and are reliable.”
© Richard Pak, CEO at Curvalux
With each passing day, as our reliance on digital networks intensifies, so does the sophistication of threats that target these networks. Our previous discussions highlighted the hidden dangers of common network devices and the steps needed to secure them. Now, we turn the spotlight on OpenWRT. More than just an alternative firmware, OpenWRT represents a shift in the security paradigm – a community-driven approach to tackling router vulnerabilities.
But what sets OpenWRT apart in this battle against digital threats? How does the community’s involvement in development lead to a more secure and resilient solution? And importantly, what can we learn from the open-source model that can be applied to enhance the security of all networked devices?
Join us as we look into how OpenWRT is setting new standards in network security, and let’s start with the simplified answer to the question – what is router firmware?
Router Firmware: The Backbone of Network Operation
Router firmware is like the brain of a router. It’s a special kind of software that controls everything the router does. It’s different from regular software because it’s made just for managing network tasks, and it has to work smoothly all the time, even when there’s a lot of internet traffic.
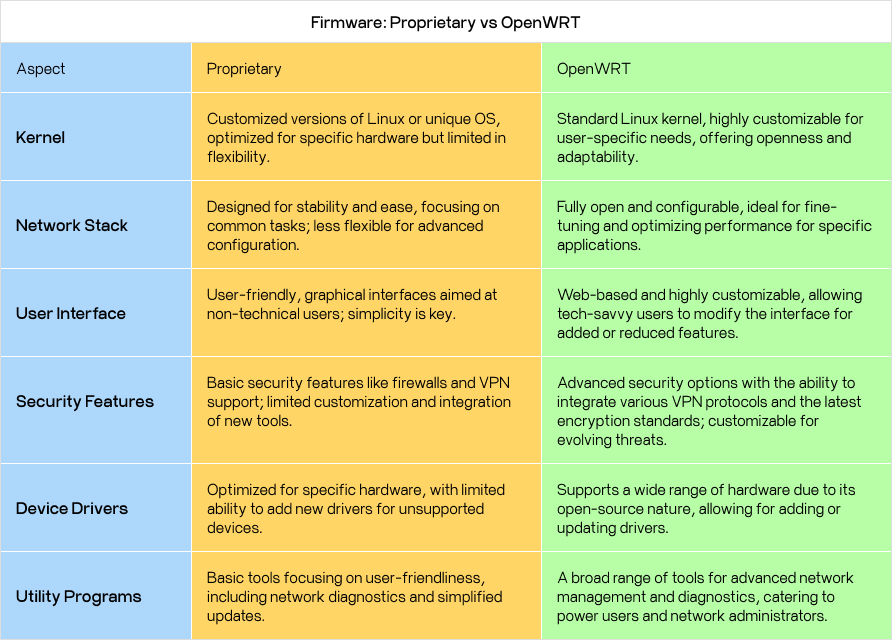
Key Parts of Router Firmware
Kernel:
Think of the kernel as the core part of the firmware. It works closely with the router’s hardware, managing important tasks like talking to the hardware parts (like NICs and CPUs), handling memory, and deciding which network requests to address first. The kernel needs to be really efficient to make sure the router can handle many tasks at once without slowing down.
Network Stack:
This is a set of software parts that send data over the network. It’s made up of different layers, each with its own job, like connecting to hardware, managing network interfaces, handling IP addresses, and making sure data gets where it’s going reliably and quickly. The network stack also handles routing packets, firewall functions, and sometimes special features like managing network quality and setting up different network segments.
User Interface:
You interact with this part to set up and manage the router. It can be a graphical interface or a web-based one. Here, you can set up Wi-Fi networks, security settings, parental controls, and guest networks. More advanced interfaces show detailed network stats, control how much bandwidth is used, and let you set up custom network rules.
Security Features:
The firmware includes security tools to protect the network from outside threats. This includes firewalls, VPN support for secure remote connections, and encryption standards for Wi-Fi security. More advanced firmware might have extra security features like systems to detect and prevent intrusions and control who can access the network.
Device Drivers:
These special programs let the firmware talk to the router’s physical parts, like Wi-Fi antennas and Ethernet ports. They turn the firmware’s commands into actions the hardware can understand. These drivers need to be really good at handling network traffic to make sure the router communicates quickly and reliably with its hardware.
Utility Programs:
These extra firmware tools help manage the network, diagnose problems, and keep the firmware current. They include tools for monitoring the network in real time, analyzing how much bandwidth is being used, checking ports, and keeping logs. Some firmware also has tools for updating itself automatically, so the router always has the latest software and security updates.
Firmware: Proprietary vs OpenWRT
Unpacking Common Vulnerabilities
“The explosion in IoT device attacks will continue regardless of current security solutions. That’s because today’s network security solutions for IoT devices fail miserably at preventing and/or detecting the root cause of these attacks: insecure coding practices and shoddy manufacturing.”
© Terry Dunlap, Former co-founder of Tactical Network Solutions and ReFirm Labs, Co-founder of Gray Hat Academy.
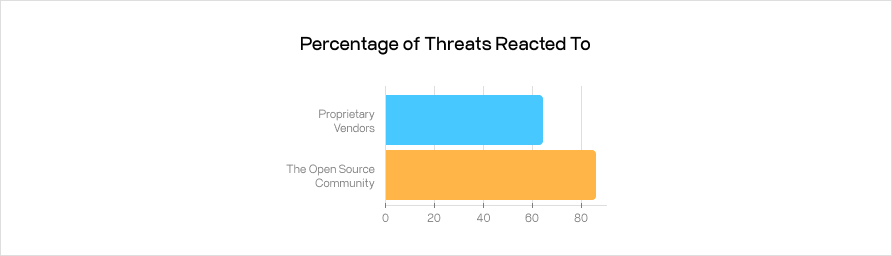
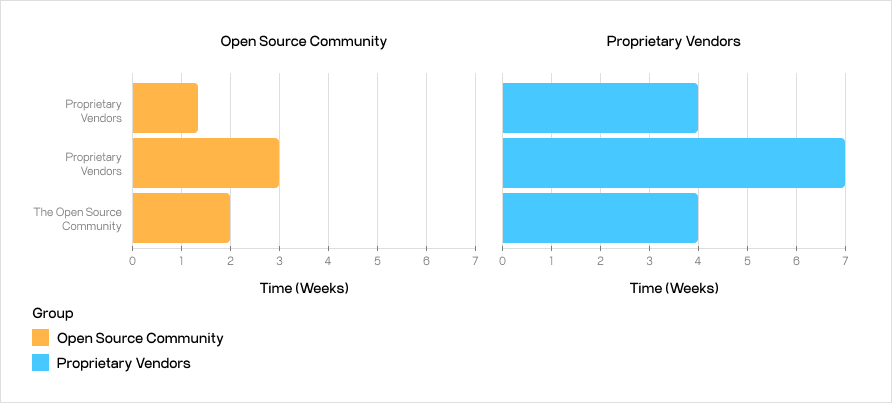
Network security heavily relies on commercial routers that often face various vulnerabilities, posing risks to businesses and individual users. While user-friendly, commercial firmware typically lacks the speed to respond to new threats quickly, open-source firmware like OpenWRT provides a more dynamic, responsive security solution. It benefits from the collective input and scrutiny of a global developer community, leading to quicker identification and fixing of security gaps, compared to the slower update cycles of commercial firmware.
Additionally, open-source firmware is transparent, allowing users and security professionals to examine the source code for possible vulnerabilities, a feature that commercial firmware, with its more closed nature, lacks. Let’s take a look at some facts.
A Statistical Perspective
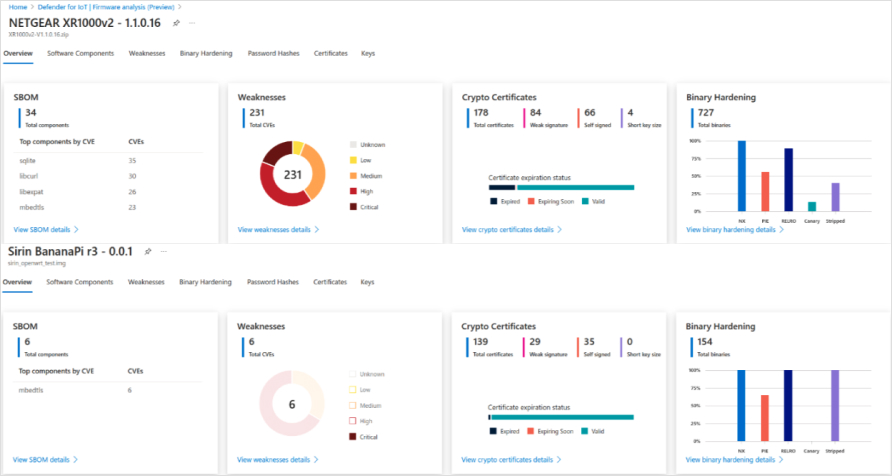
Utilizing Microsoft Defender for IoT, our analysis reveals striking differences in vulnerability statistics among popular routers. The data shows a consistent pattern of vulnerabilities across commercial firmware routers, whereas OpenWRT firmware demonstrates a notable deviation.
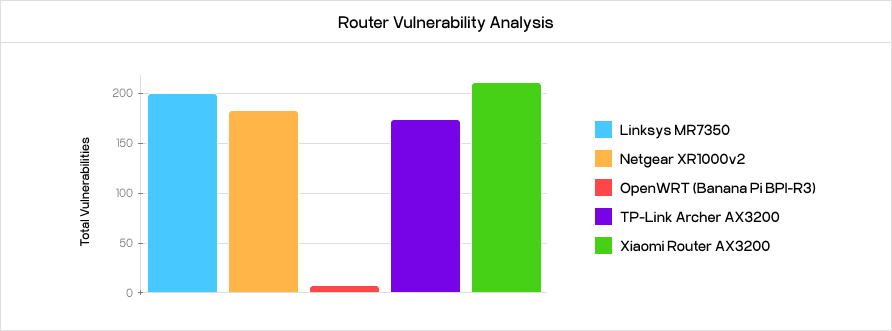
- Commercial Firmware Routers: The Linksys MR7350, TP-Link Archer AX3000, NETGEAR XR1000v2, and Xiaomi Router AX3200 all exhibit a significant number of vulnerabilities, with a total count reaching up to 201, 177, 181, and 203, respectively.
- OpenWRT Firmware: In contrast, the OpenWRT firmware on Banana Pi BPI-R3 showcases remarkably fewer vulnerabilities, totaling just 3.
Severity and Distribution of Vulnerabilities Across Platforms
As an additional result of our research, let’s categorize the vulnerabilities based on their severity to understand their potential impact better:
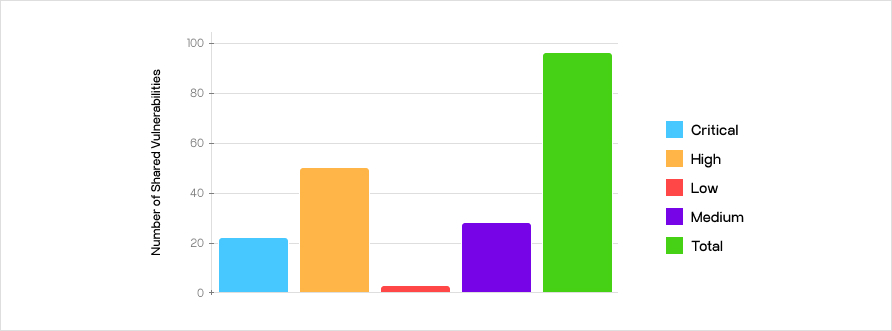
- Critical and High-Level Threats: Among the 97 vulnerabilities present across most firmware platforms, critical vulnerabilities constitute 21.65%, while high-level threats account for 50.52%. Notably, commercial products share 36 common vulnerabilities, with 23 of these being of high and critical severity.
Router Software Packages
During the research, we identified several key software packages as common sources of vulnerabilities across different router platforms. Libcurl and Libexpat, integral to router operations, harbor many vulnerabilities, accounting for 10-20% of all vulnerabilities on each platform.
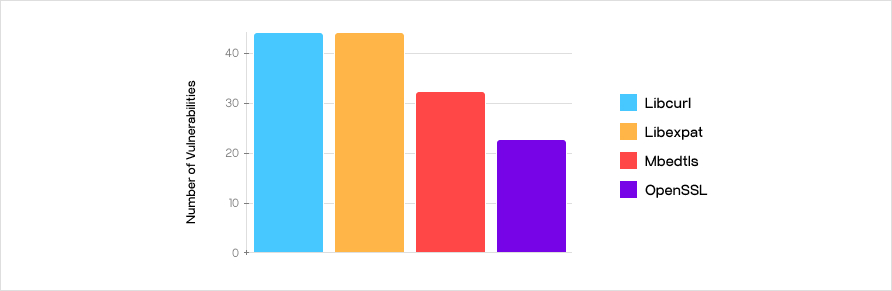
- With 43 identified vulnerabilities, Libcurl, the key for data transfer using URL syntax, emerges as a significant security concern. Its extensive application in various network functions makes it a frequent target for exploitation.
- Matching Libcurl with 43 vulnerabilities, Libexpat’s critical function in XML parsing, particularly for router configuration, places it at the forefront of potential security breaches.
- Cryptography Libraries: Both OpenSSL and MbedTLS, with 23 and 34 vulnerabilities, respectively, are vital for cryptographic operations in routers, including certificate verification and traffic encryption.
As it becomes evident, information security is a complex challenge; numerous packages contain a variety of vulnerabilities. However, these vulnerabilities are quickly identified and addressed thanks to their use in many projects and open-source code. A prime example of this is the solutions built on the current versions of these libraries, such as OpenWRT.
The Design Philosophies: Proprietary vs OpenWRT
Now, let’s try to understand why our research led us to these results. For network security, the underlying philosophy guiding the design of a router significantly influences its security posture.
Proprietary Routers: Security Behind Closed Doors
Proprietary routers dominate the consumer market and are typically developed by major corporations focusing on user-friendliness and broad compatibility. At a technical level, these routers operate on closed-source firmware – software whose source code is not publicly available. This means that the inner workings of the router’s software are a closely guarded secret of the company, ostensibly to protect intellectual property and maintain competitive advantage.
From a security standpoint, this closed-source approach has significant implications. Firstly, vulnerability discovery and patching are entirely in the hands of the manufacturer. Users depend on the company’s diligence and timeliness in updating their firmware to address security threats. This reliance can be problematic, as firmware updates are often infrequent and may not address all known vulnerabilities immediately. Also, the lack of public scrutiny means potential security flaws may go unnoticed or unaddressed until they are exploited in the wild.
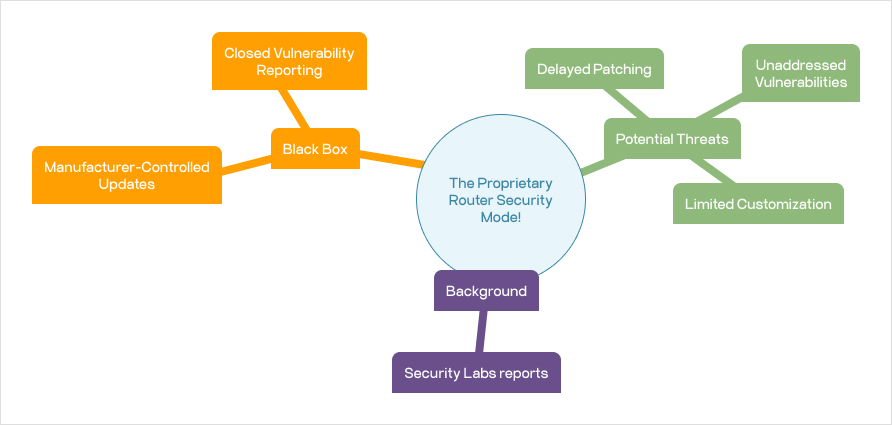
Recent reports by security labs reveal a concerning trend in the proprietary router market: a significant portion of critical vulnerabilities remain unaddressed. In fact, analyses have shown that almost a third of these critical vulnerabilities discovered have not received any response from vendors, while another substantial percentage only received generic advisories, often suggesting users contact technical support for further assistance.
Another aspect to consider is the ecosystem’s limitations. Proprietary routers usually offer limited customization options, constraining advanced users and network administrators who may wish to implement specific security measures. This “one-size-fits-all” approach can leave certain user-specific security needs unmet.
Community-Powered Security with OpenWRT
OpenWRT stands out as a prime example of open-source thinking in network hardware. It was created with the goal of giving users more control and flexibility and works in a way that is completely open and based on teamwork. Anyone can look at, change, and improve its firmware’s source code.
This openness is key to how OpenWRT handles security. By letting everyone check the code, it’s more likely that the community – which includes a wide range of users, developers, and security fans – will find and report any weaknesses. This group effort often means security problems are found and fixed faster than with closed, company-owned systems.
For example, this method was shown well when the CVE-2020-7982 vulnerability in OpenWRT’s package manager, OPKG, was quickly fixed. The community acted fast to stop a serious risk that could let attackers get around the safety checks of downloaded packages, showing how powerful working together openly can be.
Also, because the community develops OpenWRT, it can quickly respond to new threats. Security updates and fixes are released often, and being open-source means these updates can be put out quickly. Users don’t have to wait for a single company’s update schedule, they can use security patches as soon as they’re ready.
This was clear when issues in the Linux Kernel’s mac80211 and cfg80211 frameworks were quickly fixed in OpenWRT versions 22.03.2 and 21.02.5, showing the community’s dedication to staying ahead in security.
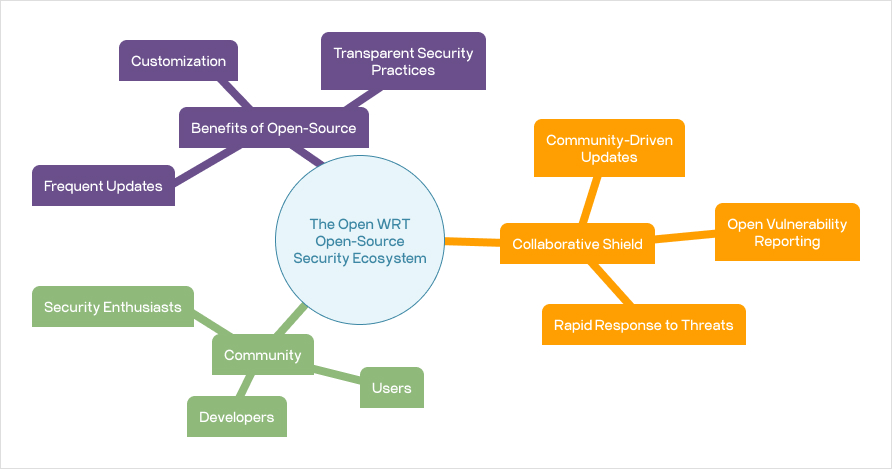
Another significant advantage of OpenWRT is its high degree of customization. Users can tailor the firmware to their specific needs, adding or removing features based on their security requirements. This flexibility extends to implementing advanced security protocols and tools, which can be integrated into the router to enhance its defensive capabilities.
Differentiating Easily Remembered Factors
Development Philosophy:
Proprietary routers are profit-driven and designed for mass-market appeal, whereas open-source routers are community-driven, focusing on customization and security.
Transparency and Community Involvement:
Open-source projects thrive on community involvement and transparency, contrasting with proprietary development’s closed, internal processes.
Security and Updates:
Open-source routers benefit from rapid, community-driven updates and a broader pool for vulnerability detection. Proprietary routers, while professionally developed, can be slower to update and less transparent about security features.
Flexibility and Customization:
Open-source routers offer greater flexibility for customization and tweaking, which is limited in proprietary models due to closed ecosystems and warranty concerns.
Making the Right Call: Proprietary or Open Source?
When selecting the right router for network security, we all need to understand the practical differences between proprietary and open-source routers. Each type offers distinct benefits and suits different user needs and scenarios.
Also, do not forget about the human factor in network security, regardless of the router type. Proper configuration, regular updates, strong password management, and vigilance against threats are key practices for proprietary and open-source routers. The effectiveness of a router’s security largely depends on the diligence and awareness of the users and administrators managing it.
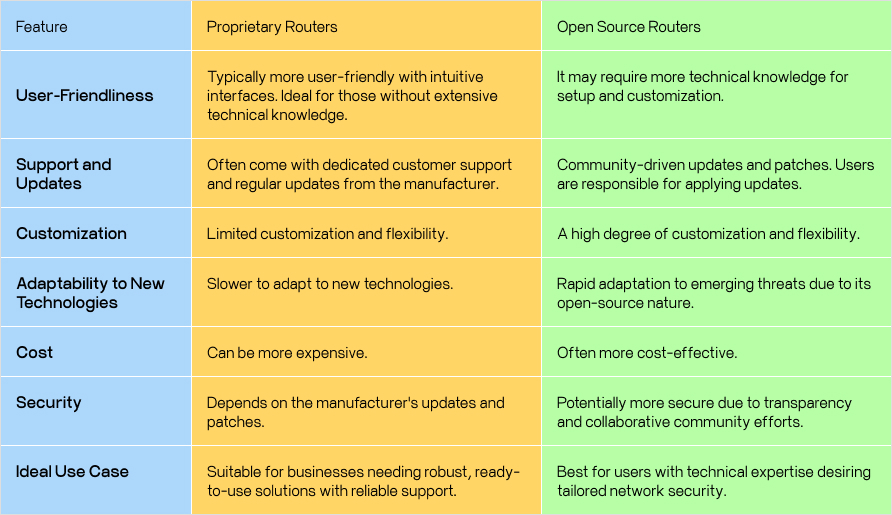
In summary, the choice between proprietary and open-source routers should be based on the user’s or organization’s specific needs, technical expertise, and security practices. While proprietary routers offer ease of use and dedicated support, open-source routers provide flexibility and rapid response to threats, requiring more technical involvement.
Securing Tomorrow: Sirin Software’s Role in Evolving Network Safety
In the fast-changing world of network security, we face new daily challenges and solutions. The growth of the Internet of Things has broadened our network reach, creating more ways for cyber threats to enter. Emerging technologies like Artificial Intelligence and Machine Learning are key in identifying and predicting new threats by studying network behaviors, but cybercriminals can also use these technologies to develop complex attacks.
The increase in remote work has made secure network access a priority. Tools such as VPNs, secure Wi-Fi, and encryption are vital for safe remote connections. Our expertise in creating secure and easy-to-use network solutions, including VPNs and encrypted communication systems, is invaluable in this new landscape. We help businesses confidently face these challenges.
The move towards community-driven development is becoming more popular. This method encourages technological progress and a culture of shared knowledge and active collaboration. Sirin Software is a part of this movement, contributing to and using community projects to improve our services. We stay ahead in network security trends, offering our clients the latest solutions. Notably, as part of our dedication to top-tier security, we have partnered with Microsoft as early adopters of their Defender for IoT technology. This collaboration brings comprehensive IoT device and network protection to our portfolio and underscores our ongoing effort to offer robust, up-to-date security solutions.
Looking ahead, we see network security as a shared task. Every update we install, every strong password we create, and every smart choice we make strengthens our digital world. Sirin Software is dedicated to this path, providing the tools and knowledge needed for a safer digital future. We urge you to remain informed, active, and forward-thinking in your approach to network security. In the digital world, being well-informed and prepared is the best defense.