Wi-Fi Router Vulnerabilities: What's Lurking Inside?

With digital connections expanding and reliance on the internet deepening, cybersecurity stands as an issue. As we digitize operations and increase interconnectivity, the range of potential threats grows and evolves. Our private data, business operations, and even national defense systems, all exist within this threat landscape. Routers, especially Wi-Fi routers, play an important role here, acting as the primary defense line in a battle of escalating cyberattacks.
“It is impossible to build reliable protection without understanding the weaknesses of each element. For network security, the basic component is network equipment. This element’s unreliability can allow attackers to achieve their goal regardless of other protection mechanisms.”
© Serhii Sakhno. Senior SWE. Sirin Software
Your humble router: The secret battlefront
Wi-Fi routers are integral in our personal and professional lives, acting as key access points for data and protecting us from harmful entities. Their function extends beyond being simple gatekeepers, making them important elements of our cybersecurity strategies. The weaknesses of these devices warrant careful attention, not merely due to the increase in remote work linking home routers to business networks, but primarily because of a more widespread and harmful issue: the formation of botnets – automated, interconnected systems that are often used to execute large-scale attacks on commercial and government networks. The problem is not restricted by geography or organization size. It reaches far beyond whether a company employs remote workers. Any router, anywhere, can become a component in this extensive, malicious network.
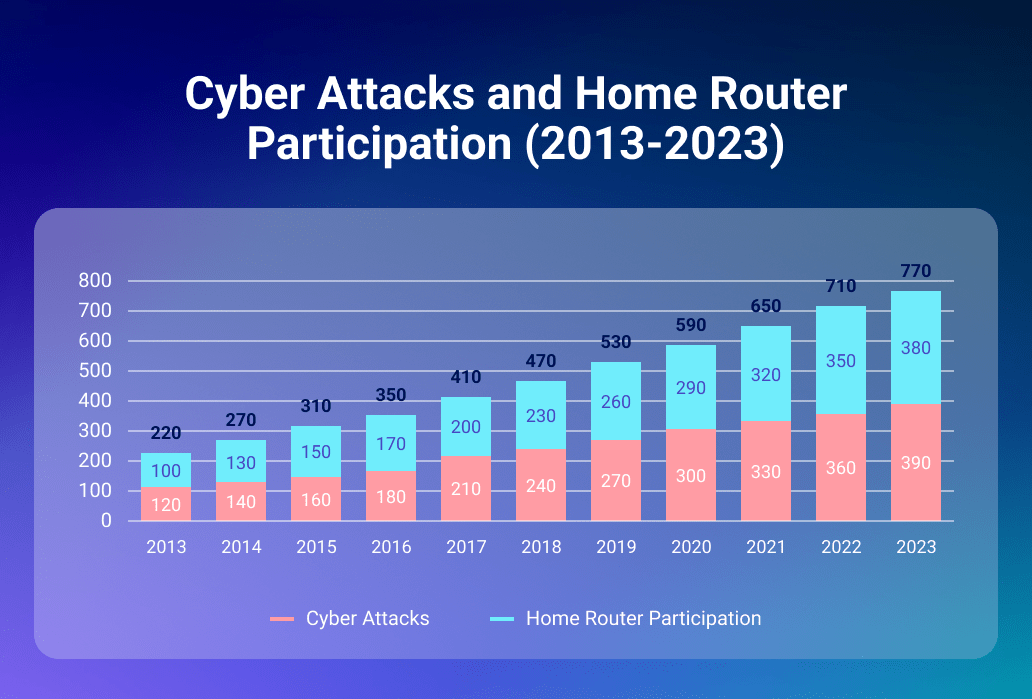
Our home routers have become not only our personal portals to the internet but also potential points of exploitation that can be turned against us, threatening the stability of larger networks. That is why we want to share with you the methods and the results of our research.
Invisible walls: The puzzle of proprietary security
Navigating closed-source solutions often leads to a lack of transparency and control over the product’s design, code, and firmware. These solutions, like black boxes, keep the internal processes secret, leaving both commercial and personal users dependent on vendor promises. For the vast majority of the common home WiFi routers, users are largely at the mercy of these vendors, trusting they’ll not only create strong firmware but also promptly release security patches and manage user data judiciously. Legal agreements generally mediate this trust, yet they often shield vendors, leaving users vulnerable to the fallout of data breaches.
This obfuscation introduces two significant issues. First, closed-source solutions often bar comprehensive security evaluations, making it tough to analyze firmware for vulnerabilities. Consequently, it’s challenging for users or independent researchers to confirm vendors’ security claims or preemptively pinpoint and address potential threats. Second, vendor lock-in arises due to the software’s proprietary nature, which constrains user options for customization and security upgrades.

Addressing these limitations, our research focused on finding security tools that could bridge this gap. In response, as our team has joined Microsoft’s Firmware Security Partner Network as an early adopter of Microsoft’s Defender for IoT, we chose this tool as a robust security solution applicable to IoT devices, including WiFi routers. Now, with the help of this technology, we are able to perform firmware scanning that provides missing insights and identifies issues before they become a compromise.
Battle of the routers: Firmware security analysis
Being fervent proponents of robust network security, we undertook a comprehensive review of proprietary firmware across different vendors. This task posed a challenge given the inherent intricacies of proprietary firmware. Its closed-source nature made conventional code audits unfeasible as we lacked access to the firmware’s source code.
How we do it: A Peek into our review methodology
Our job was to get a good grasp of Microsoft’s Defender for IoT, a complex tool for checking out firmware. We zeroed in on each of its features, which meant we needed to dig deep into how this particular function works. After getting hold of the latest firmware packages from vendors, we loaded these into the tool system, making sure each one matched perfectly with the tool’s settings. This careful setup required a lot of technical tweaks to get the vulnerability checking right.

We utilized the Firmware Analysis as a key part of Defender for IoT for our research. This feature scans the firmware thoroughly for possible security holes. The first scan creates a list of potential weaknesses in the firmware. The tool then uses this list to compare with well-known vulnerability databases, like the Common Vulnerabilities and Exposures (CVE) list. This comparison process is very detailed, aiming to fully understand each possible vulnerability. Each identified vulnerability is evaluated based on how severe it is, how likely it is to be exploited, and what impact it could have on the system. This tool offers a risk-level breakdown of these vulnerabilities, which gives a clear overview of the firmware’s security situation.

We also paid close attention to checking out-of-date or compromised libraries within the firmware. These libraries are vital to how the firmware works and, therefore, its security. We looked closely at each library’s role within the firmware, assessed the vulnerabilities linked to its version, and understood what these weaknesses could mean. Our goal was to find libraries that might have had vulnerabilities that hadn’t been patched or could be used as a launch pad for a cyberattack.
Comparative security analysis of popular WiFi routers
Here’s the part of the data from our investigation, presented in a simple format:
| Router | Date | CRITICAL Absolute /Relative |
HIGH Absolute /Relative |
MEDIUM Absolute /Relative |
LOW Absolute /Relative |
Total |
| Linksys MR7350 | 2021-02-21 | 33/18.86% | 82/46.86% | 54/30.86% | 6/3.43% | 175 |
| TP-Link Archer AX3000 | 2023-03-29 | 29/16.76% | 75/43.35% | 63/36.42% | 6/3.47% | 173 |
| NETGEAR XR1000v2 | 2023-01-13 | 47/19.75% | 97/40.76% | 79/33.19% | 15/6.30% | 238 |
| Xiaomi Router AX3200 | 2023-02-25 | 30/14.78% | 102/50.25% | 63/31.03% | 8/3.94% | 203 |
Of course, these routers have different features and capabilities. But the goal of this investigation is to analyze their security aspects, not their function. Upon reviewing the data, we found some noteworthy results. The NETGEAR router showed the worst security performance, both in terms of total vulnerabilities and the number of critical and high-risk vulnerabilities. The routers from Linksys and TP-Link demonstrated the least number of exposures. Interestingly, the TP-Link router presented lower rates of critical and high-risk vulnerabilities than the Linksys router. The Xiaomi router occupied an intermediate position in terms of total vulnerabilities. It had the same rates of critical vulnerabilities as the previous two routers, both in absolute and relative terms. However, it showed the highest rate of high-risk vulnerabilities.

As we can observe, all the analyzed firmware had a similar distribution of exposures at each level relative to the total count. The absolute count of vulnerabilities showed only minor differences. That means that strong cybersecurity is a must in today’s connected world, and Wi-Fi routers are key. They have unique strengths and weaknesses, but no router is completely safe. However, being aware and defending against threats can lessen the risks. We need to keep learning and adapting to quickly changing threats. Remember, cybersecurity is everyone’s job. A safer online world protects not only our data but also our way of life.
The purpose behind our pursuit
At Sirin Software, our effort is all about innovating and striving for improvement in network security solutions. We pride ourselves on our profound expertise in network security, and our commitment to this pursuit is beautifully embodied in one of our notable projects – the SD-WAN solution.
The task was to build a system using a Linux base, allowing multiple Internet channels to function simultaneously. We crafted a unique Linux kernel, incorporated a user-friendly web interface for effortless system configuration, and added a VPN for secure communication. Despite facing a steep road ahead, with challenges like ensuring the system’s robust performance under high loads and creating an easy-to-use web interface, we stayed the course. The result? A solution that promised efficient use of various Internet channels, uninterrupted Internet access, and easy configuration – all under a security umbrella.
Yet, we know our journey doesn’t end here. We continually refine the solution, introducing new features and optimizing it to meet even higher demands. Our focus is on enhancing the system’s flexibility to accommodate diverse network conditions.
Plotting the path for future studies
Our mission is to keep advancing our knowledge. That’s why we plan to widen our research to include a variety of systems, covering both open-source and proprietary solutions. The aim is to deepen our understanding of router firmware security landscapes and share it with you.
Our future studies are planned with a detailed strategy in mind. We aspire to examine the systems more closely, explore the existing vulnerabilities, and dissect the strengths and weaknesses of different router firmware. The goal is to magnify our understanding and improve these systems’ security.
We’re determined to contribute to the cybersecurity world significantly. We strive to offer practical insights and strategies that could shape the development of more secure networking devices. At Sirin Software, we are not just doing a job – we are driven by our shared passion for innovation in cybersecurity.
FAQ
What can I do to protect my home router?
Start by changing the default username and password to prevent unauthorized access. Regularly update your router's firmware to fix potential security vulnerabilities. Use a strong encryption method like WPA3 for your Wi-Fi and disable features you don't need like remote management or UPnP. You can also set up a guest network for visitors to prevent them from accessing your main network. Additionally, you can consider using a VPN for enhanced data protection.
What's the difference between security vulnerabilities?
They vary based on potential impact, how they can be exploited, and the difficulty in mitigating them. They can be classified into different categories, like critical, high, medium, and low, based on their severity. Critical vulnerabilities are the most dangerous as they can lead to significant damage such as data breaches or complete system takeover if exploited. High vulnerabilities are less severe, but still pose a considerable risk. Medium and low vulnerabilities are less severe but still need addressing. Each vulnerability also has a unique identifier called a CVE number, used to track and resolve it.
I use my router only for home entertainment. Why should I be worried?
Even if you're using your router just for home entertainment, its security is still important. Hackers can exploit vulnerabilities in your router to gain access to your home network. This could allow them to take control of your smart devices, steal your personal information, or use your network for illegal activities. They could also interrupt your entertainment by slowing down your internet speed or even blocking your access. To avoid such risks, it's important to secure your router, regardless of how you use it.
Are there any open-source home routers?
Indeed, open-source home routers exist. They use modifiable open-source firmware like DD-WRT, OpenWrt, and Tomato. Certain routers come equipped with this firmware, whereas others may require manual installation. Open-source routers often grant users more network control and can have additional features that proprietary routers lack. However, they also have drawbacks. Being open-source means these routers rely heavily on community support for updates and patches. If the community is not active, security issues may not be addressed promptly. Furthermore, setting up and configuring these routers can be challenging for those without technical expertise, making them less user-friendly than some proprietary options.